Part 1 of the blog series discussed the importance of having a scalable access control solution that meets the plethora of requirements for modern enterprises — functional across geographies, use cases, and for petabytes to terabytes of data across multiple systems without negative TCO impact and performance degradation. Part 2 will explore other practical considerations — that CEO and co-founder of Privacera, Balaji Ganesan shared in the latest Business Intelligence Journal by TDWI — when evaluating data access control and privacy solutions.
A Reality Check: The Burden on Human Resources
It is inevitable that your enterprise will have a team responsible for deploying, managing, and executing whatever processes and tools are selected to do the job. However, enterprises cannot expand resources to manually implement a data privacy and security program at the rate it is needed. It is untenable for an enterprise to manually bring all the different systems together to ensure consistent data access control. Moreover, balancing the dual mandate of complying with regulation and making data widely available company-wide presents another challenge across different teams.
Putting Best Practices to The Test With Your Access Control Solution
When so much complexity is involved in the implementation, yet consistent adherence to regulatory requirements is unyielding, a single interface that brings together disparate systems into a consistent program creates synergy and offers a practical approach.
Additionally, a unified approach accelerates data privacy by creating a platform that provides encryption, data masking, and data filtering capabilities. This enables companies to protect their data while it is at rest or in motion as well as leverage insights from it by masking or filtering sensitive data. IT teams are relieved of the responsibility to install, manage, and update separate encryption/decryption tools. When there is a unified approach to both access control and encryption, companies can leverage a solution that can be deployed quickly and fuels accelerated outcomes. This may seem obvious, but the caveat is to implement technology that can be deployed quickly while meeting all the requirements.
Deployments that require a significant amount of time setting up underlying infrastructure can obviously delay and set back any program. Yet, take TCO into consideration. Trade-offs to consider include how quickly the initial deployment can occur, how quickly various teams can use the deployed solution, and how soon the system can scale to a complete enterprise-wide deployment.
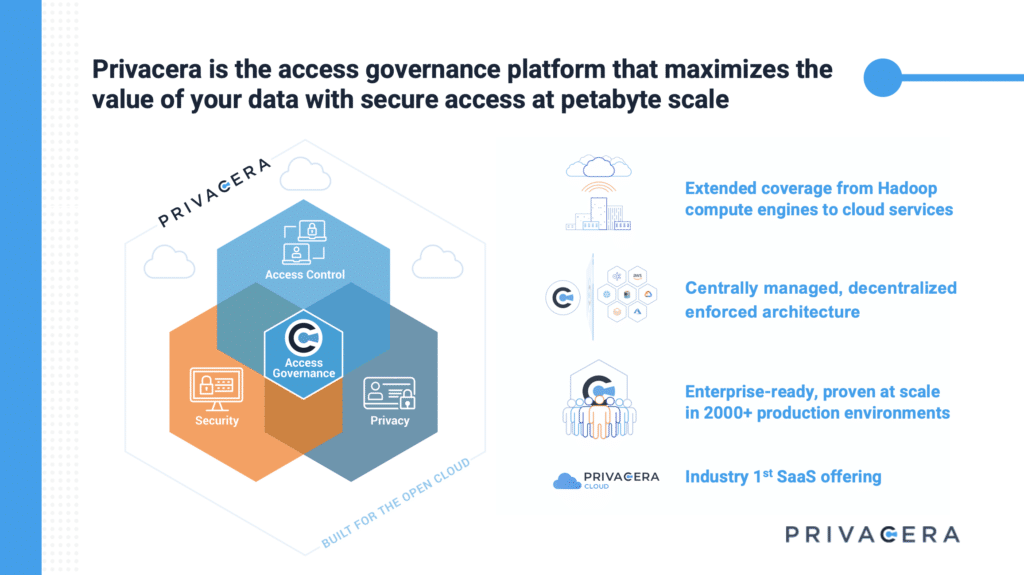
Can your data privacy and security solution be rolled out in a day? Can you leverage existing processes and policies so that you can immediately apply privacy policies? How quickly after your initial deployment can the full volume of your enterprise data be managed? Can you clarify what a “quick deployment” truly means with respect to the full scale of requirements discussed above? As with most software solutions today, one of the fastest ways to scale is to consider a cloud-based SaaS solution, such as PrivaceraCloud, because it alleviates the need to provision or manage the infrastructure and provides a fully configured access governance solution to get started immediately.
Beyond the initial deployment, you need to know how quickly and easily upgrades can be implemented. How often are upgrades required, and how long does it take to update software and why? For example, when utilizing a data virtualization architecture for data security, you will require new engineering development for every new analytics service/ data store/ feature/ capability that becomes a never-ending hamster wheel of upgrades that needs to be rolled out into production environments across the enterprise.
Moreover, by building a virtualized layer as part of the implementation to accommodate different data sources, data virtualization-based access control products can easily be a single point of failure that severely disrupts data operations. The virtualized layer intercepts all data requests to validate whether users have access to data or not, impeding performance. Additionally, users will not be able to access the data if the virtualized platform experiences outages or downtime, as permissions must be validated in the virtualized platform. Users don’t run into the same availability issue with Privacera because we don’t interfere with the path of existing databases and data requests go straight to the associated system.
Another problem with the virtualized layer is that any changes to the upstream source data repositories must be reflected into the virtualized layer. This leads to the creation of thousands of views in the virtualized layer that leads to a maintenance nightmare. Again, users don’t run into the same issue with Privacera’s architecture because we have lightweight plugins that are embedded with the services and perform a quick validation of whether the user has the permission to access requested data or not. The plugins are kept current by inheriting the policies from a policy server. Privacera is not in the path of data and doesn’t require any changes to the tables or user behavior, as is the case with data virtualization-based access control products.
Looking Ahead: Develop A Thorough and Comprehensive Plan
Finally, your enterprise should conduct a thorough and comprehensive proof of concept (PoC) that tests the entirety of requirements for different teams and systems. Define a realistic scope that emulates the scale and complexity of your final production deployment.
This may seem counterintuitive because a comprehensive PoC can take longer than a shorter, more perfunctory evaluation and thus delays progress. However, when you deploy an enterprise-wide data privacy and security program, you have no time for an iterative, “fail-fast, fail-often” approach. Deploying a solution today in a limited capacity and testing to see if it works — just to have to remove it and try something else — ultimately delays a comprehensive program. To avoid your privacy initiative from being derailed after it is implemented, it’s critical to conduct a thorough evaluation up front.
To learn more about Privacera, visit Why Privacera? or contact us to schedule a quick call.