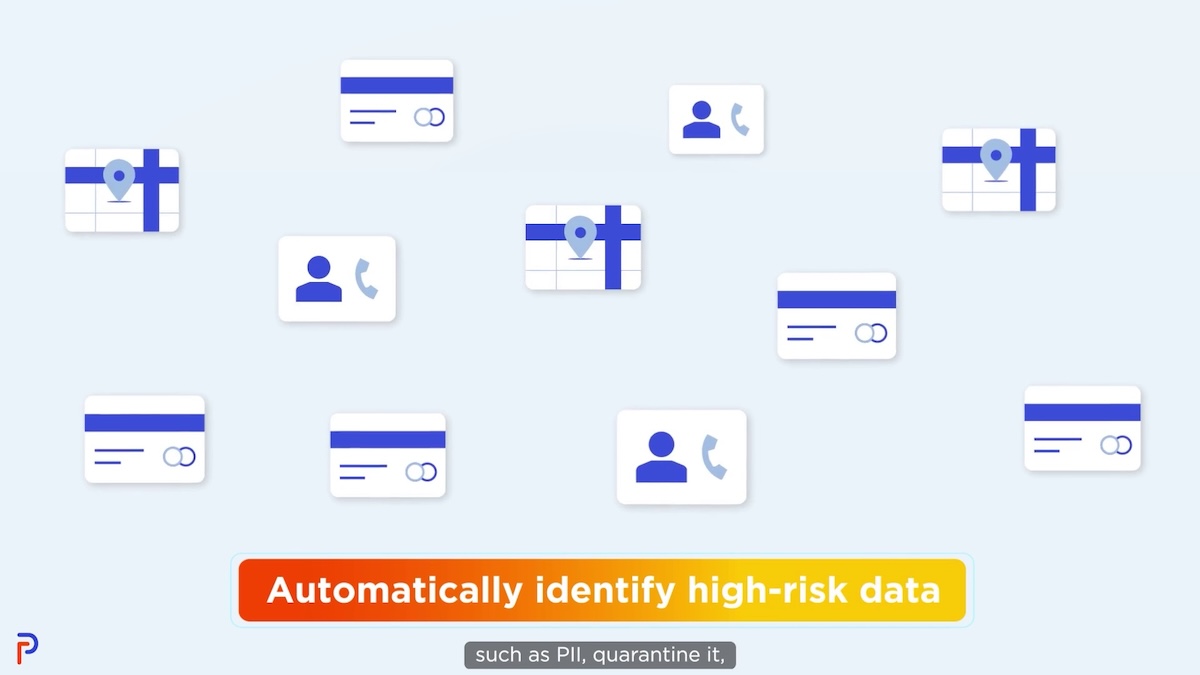
Privacy professionals must manage an exploding volume and diversity of data. The sheer volume is challenging enough. The challenge is compounded by the need for privacy to be extended to increasingly complex internal and external ecosystems. The only way to succeed is to automate PII discovery. Automation must also be paired with simplified policy creation and control to ensure compliant, authorized, fair, and legitimate processing of personal information and private data. Succeed from a privacy impact assessment to global policies and global controls.
Key Benefits:
- Discover PII Automatically
- Protect Data Across Data Systems
- Develop Global and System Policies
- Manage and Audit Proactively
Discover PII Automatically Across All Data Systems
Automation starts by automatically discovering exposed PII across all data systems and the entire data estate. Our solution determines data elements that need to be depersonalized or de-identified of sensitive data elements via prebuilt rules. Critical data elements include names, addresses, phone numbers, and national or tax identification numbers. Our solution enables data privacy professionals to determine class attributes for access authorization, including roles, policies, and rules for access.
Protect Data Across All Data Systems
Implements global controls simultaneously across all systems instead of system by system using Attribute and Tag based access controls and compliance workflows. This ensures transparent controls and consistent enforcement. Privacy can now ensure privacy rules are entered into metadata repositories according to privacy policies.
Develop Global and System Policies
Protects personal information by codifying privacy policies and controls. Unauthorized access and inappropriate behavior is controlled by defining global and system controls as well as roles, behaviors, data classes, and locations. Easily attributable definitions, efficient controls, and global policies are key to automating consistent policy implementation and enforcement.
Manage and Audit Proactively
Supports the principles of Privacy by Design, including the proactive management of privacy across the end-to-end lifecycle. This approach allows for continuous improvement, measuring conformance with policies and policy-build processes, and the auditing of policies and controls.